Why Fast Networks are Secure and Pirated Software is Not
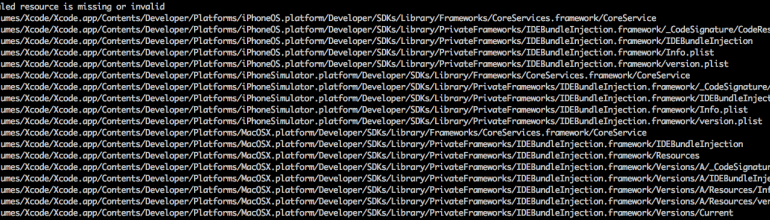
Conventional wisdom says that curated app stores like Apple’s are more secure than wild west downloads from random servers. This is true, of course, but being more secure doesn’t mean they’re perfectly secure. In September, Palo Alto Networks reported that some popular Chinese apps in the Apple store were infected with malware, and the report turned out to be true. The attackers invented a somewhat novel means of getting their malware into the Apple store: they infected versions of Apple’s developer tools and uploaded them to popular file sharing sites in China. Chinese developers downloaded the files in question, parts of Apple’s XCode toolkit, and used them to compile their apps. The apps produced with the corrupted tools also carried the malware, so the files uploaded by legitimate developers to a legitimate app store were infected. After Palo Alto’s report surfaced and was verified, the file sharing sites took down the infected version of XCode (known as “XCodeGhost”).
Several things had to happen for this hack to work, so its odds of success were pretty low:
- File sharing sites had to accept ostensibly pirated copies of Apple’s tools for distribution without license.
- Legitimate Apple app developers had to choose a pirated copy of XCode from a local server over the legit one hosted in the US.
- Development teams had to use QA procedures that failed to verify the legitimacy of the tools and libraries use to build their code.
- Apple’s process had to fail to detect corrupted XCode libraries.
- Users had to love the apps.
According to a somewhat one-sided story in ZDNet, Chinese developers prefer to download Apple tools from “file sharing” (the correct term is “piracy”) sites over Apple’s official site because local sites download faster. This is certainly plausible because there’s a lot of traffic flowing between the US and China, and it all has to pass through The Great Firewall before or after it wends its way through 6000 miles of undersea cables. Fiber optic cables are fast as long as they’re properly provisioned, so I’d guess the Great Firewall is a great motivator to use local sites rather than international ones.
File sharing sites thrive on unlawful activity, so they’re not going to look for malware in the code they accept for “sharing”. It’s already unlawful code anyhow, so who cares about a little malware here or there? It should be understood by the developers that pirated code can’t be trusted, and their managers should understand the motivation to use pirated code and take steps to maintain an official copy of Apple’s official tools. These are not small-time developers, they’re some of China’s biggest:
The App Store malware breakout is worse than first thought, however, with security experts claiming today that WeChat, a hugely popular messaging and social networking app, and Didi Kuaidi, Uber’s chief rival in China, carried the threat. The attackers, FORBES understands, are hunting for iCloud login details amongst other data.
It’s always good to change your Apple passwords if you have any.
The XCodeGhost attack teaches some important lessons about security: even the most secure system can be hacked; and it’s not enough to authenticate the user, it’s necessary to authenticate the code the user is running. The latter lesson should have been obvious insofar as it’s the code that carries the malware, not the user. But user authentication is a proxy for code validation because it’s easier.
Users don’t change as rapidly as code does, and users are relatively uncomplicated compared to code. In some sense, every shortcut is an attack vector, and this is probably the shortest shortcut of them all.
The most secure systems can be hacked because software always has bugs, and the entire system from apps to tools to stores to end users is incredibly complex and impossible to validate completely. There are computer science proofs of the proposition that software can never be guaranteed to behave correctly.
So what happens as we expand mobile apps from their relatively vulnerable state today into an IoT world where code has to run in smaller environments and programmers have to resort to shortcuts in their code to get around device limitations? And what happens now that hackers know the Apple ecosystem can be compromised by impatient developers abetted by piracy sites? And what happens when devices become more uniform?
All of these things increase the motivation for attackers to target new, cheap. and useful little devices that do simple things for us. Which says we need a better security model than the Internet and our app stores can offer.
So this is yet another wakeup call about a problem that has had far too many wakeup calls already. Perhaps we need a revolution in app design and network architecture.
Stay tuned for some promising candidates to lead that revolt in the weeks to come.