A Technical View of the Title I/Title II Debate
The FCC’s review of the regulatory status of broadband Internet Services focuses the spotlight on the distinction between Title I and Title II services. Title II is meant to apply to the transmission of information while Title I applies to the processing of information. The regulatory debate largely revolves around the nature of the transmission/processing distinction (TPD).
Background of the Transmission/Processing Distinction
This distinction dates to the FCC’s first Computer Inquiry in 1966, distinguishing basic from enhanced network services. In its original meaning, basic service connected telephone calls and enhanced service encompassed services such as voice mail that added processing, storage and retrieval.
The first Internet Service provider, Barry Shein’s The World, was classified as an enhanced service when it went live in 1989. As it relied on modems and the existing telephone network, The World clearly did more than simple transmission. Dialup ISPs are still considered Title I services today.
The FCC classified xDSL service under Title II in 1998. This decision had more to do with xDSL as a transmission system than with services enabled by xDSL such as Internet service. In 2002, the FCC classified cable modem-based Internet service under Title I, recognizing its similarity to the services provided by dialup ISPs.
In 2005, the FCC applied the Title I classification to Internet Services provided over xDSL. If we accept the premise that Internet service is separable from its means of transmission, it follows that Internet Service was a deregulated Title I/enhanced service from its inception until the Open Internet Order of 2015.
Where to Draw the Line
In 1966, the nature of the TPD was clear to the FCC. Transmission was an analog service that simply moved electromagnetic energy over a wire. Processing was the realm of everything else, including telephone handsets, answering machines, fax machines, and modems. But reality is not as tidy as the regulatory mindset.
The progress of digital convergence brought out the ambiguity in the FCC’s historic distinction. The telephone network became a digital system except for its traditional analog edge, and the silos between telephone, cable TV, and mobile crumbled. The Internet was designed to run over a variety of transmission systems, and even to mix and max systems that were once incompatible. Communication networks now use the same technologies used by network-enabled services.
The devices that convert digital bits to analog waves are known as “digital signal processors”. Transmission in today’s all-digital networks is not truly separable from processing because there’s no transmission without processing. And on a routed packet network like the Internet, there’s no transmission from end to end without transient storage and retrieval at each hop as well.
DSPs are found in every modern modem and network interface. It would be reasonable to draw the line between processing and transmission between DSPs and the analog circuitry in computer interfaces that connect to wires and antennas. Drawing the line inside the interface limits the scope of Title II to wires and permits the deployment of new forms of modulation as well as competitive Title I services.
We might also draw the line between the wires themselves and the poles and conduits that carry them. Wires, it might be argued, are tightly bound with DSPs and are therefore simply extensions of the processing realm.
Conduits can carry a variety of wires: bundles of telephone twisted pairs, coaxial cable TV wires, or various kinds of optical fiber. Limiting the scope of Title I to conduits and utility poles would facilitate the installation of new networks.
The Network Management Loophole
The devices that connect homes to telephone and cable company offices are known as DSL Access Multiplexors (DSLAM) and Cable Modem Termination Systems (CMTS). These devices accept and release information frames consisting of addresses, control options, and user data.
Some regulatory regimes provide open access for information frames. This framework is necessary to the unbundling cable modem services because one and only one CMTS can service the community of users in a cable neighborhood. Similar regimes provide frame-level access to DSL networks because advanced forms of DSL use a technology known as “vectoring” that requires coordination across copper pairs in the same conduit.
The TPD can be drawn at the frame level. But considerable processing is required for frame transmission because frames are bundles of bits that must be coordinated across users for reception to be successful.
Regulators have created a loophole for this view of transmission by treating processing activities that facilitate transmission as network management necessary to transmission. But the network management exception requires a coherent definition of processing for the sake of transmission versus processing for all other purposes.
The Network of Networks Conundrum
The TPD tends to assume that a single network provides all the transmission. This was most often the case in the heyday of the telephone network, when most calls were local. Long distance calling combined two networks using the same technology, so in practice the calling network did all the management. International calling was more complex, but fit the basic paradigm.
The Internet operates in an entirely different way, however. It is a system whose function is to interconnect tens of thousands of networks with a minimum of assumptions about the characteristics of any given network. Internet interconnection requires each network to handle information in a given format: the Internet Protocol datagram. It also requires networks to signal accessibility of members in the form of an agreed-upon system of announcements. And most importantly, it requires mutual agreement to interconnect.
Interconnection agreements typically specify information sharing protocols such as Border Gateway Protocol (BGP) as well as financial and traffic volume conditions. Internet interconnection is typically asymmetrical, with each network passing traffic to the other network as soon as possible; this is known as “hot potato routing”. In practice, Internet networks pay most of the cost of receiving packets and little of the cost of sending.
Internet service providers and Internet edge services are more functionally overlapped than the networks that occupied the minds of the regulators who devised the classical TPD in 1966. Today, each ISP and each edge service provides a mix of transmission and processing.
The Collapse of Reasoned Argument
Functional overlap leads to some fairly comical declarations: In the court challenge to the 2015 Open Internet Order, the FCC argued that Domain Name Service (DNS) is network management when provided by an ISP but Title I information service when provided by other firms:
When used by broadband providers, DNS and caching are tools that are used “for the management, control or operation of a telecommunications system or the management of a telecommunications service”—and by the terms of the Communications Act, excluded from the definition of “information service”…[¶5]
Not surprisingly, the hapless DC Circuit agreed with this assessment. This is because the lawyers failed to appreciate the fact that the only network “managed” by DNS is the unregulated network operated by the edge service.
How DNS is Really Used
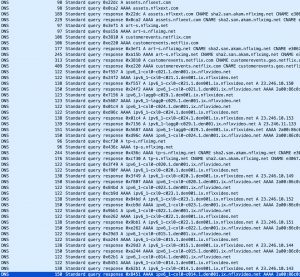
Before a user plays a Netflix video, a series of 10 – 25 transactions takes place between the Netflix player in the home and various servers inside the Netflix network. Netflix determines the nature of the user’s device, the speed of the user’s network, and the options in the user’s Netflix subscription; 4K video steaming costs more than HD format.
Armed with this information, Netflix chooses a video server and filename that best fit the factors. What started with a query to Netflix.com finally comes down to a lookup of something like ipv6_1-cxl0-c014.1.chi001.ix.nflxvideo.net.
These transactions are all mediated by DNS, but the only network affected by them is the one owned by Netflix. If DNS is a routing function as the FCC claims, its powers are limited to routing within unregulated networks.
In fact, DNS is provided by ISPs for the sake of the networks with which the ISP interconnects. Netflix stores its server names and addresses in ISP DNS databases and retrieves them as it needs. If this is “network management” it’s not the type of network management imagined by regulators in the ‘60s and ‘70s. In fact, DNS did not exist until the late ‘80s.
TPD Debate is About Network Management
The Title I/Title II debate continues because it can’t be resolved until network management is fully understood and properly defined by regulators. The 2015 Open Internet Order uses the term in a variety of contexts to mean a variety of things.
The order describes throttling and paid prioritization as network management [¶9,18]. It attaches “reasonable network management” exceptions to each of its bright line rules except the blanket ban on paid prioritization:
“Paid prioritization” refers to the management of a broadband provider’s network to directly or indirectly favor some traffic over other traffic, including through use of techniques such as traffic shaping, prioritization, resource reservation, or other forms of preferential traffic management, either (a) in exchange for consideration (monetary or otherwise) from a third party, or (b) to benefit an affiliated entity. [¶18].
It requires disclosure of each ISP’s network management practices, but doesn’t define the term itself. The only guidance the order offers on what shall be considered a network management practice is an equally vague reference to “tailored network security practices”[¶85]. Are these to be distinguished from “random network security practices”?
In the end, we’re left with nothing more than the declaration that: “A network management practice is a practice that has a primarily technical network management justification, but does not include other business practices”[¶32].
Network management is the 2015 Open Internet Order’s “Get Out of Jail Free” card.
Resolving the Dilemma
Even if Congress steps into the Internet regulation debate with a set of bright line rules, the lynchpin of the discussion will not be secure until we clarify the meaning of “processing required to manage a telecommunications service.” Engineers understand network management to include diagnostics, troubleshooting, damage mitigation, and error recovery.
We do not understand it to mean “service differentiation,” “service definition,” or “service provision.” Thus, prioritization is not a network management activity, it’s an offered service that adds value to simple transmission. Similarly, DNS is not necessary to the management of a network, it’s a part of the interconnection deal offered to partners and to services running on their own networks that have value for the ISP’s customers.
Many parts of the bundle of services offered by today’s ISPs are information services, and it’s disingenuous and reductive to claim that such services are simply means of isolating problems and deploying mitigations. The FCC’s mistaken use of the notion of network management suggests working backward from the goal of Title II classification to the best justification that could be found.
[Note: Edited 6/9 for clarity.]