Anna Gomez on the National Spectrum Plan
Richard Bennett0
Jayne Stancavage on the Global Spectrum Pipeline
Richard Bennett0
Shane Tews on Filling the Spectrum Pipeline
Richard Bennett0
Mary Brown on Building a Spectrum Pipeline
Richard Bennett0
Will Rinehart on Broadband Part Two
Richard Bennett0
Will Rinehart on Broadband Infrastructure and Inclusion
Richard Bennett0
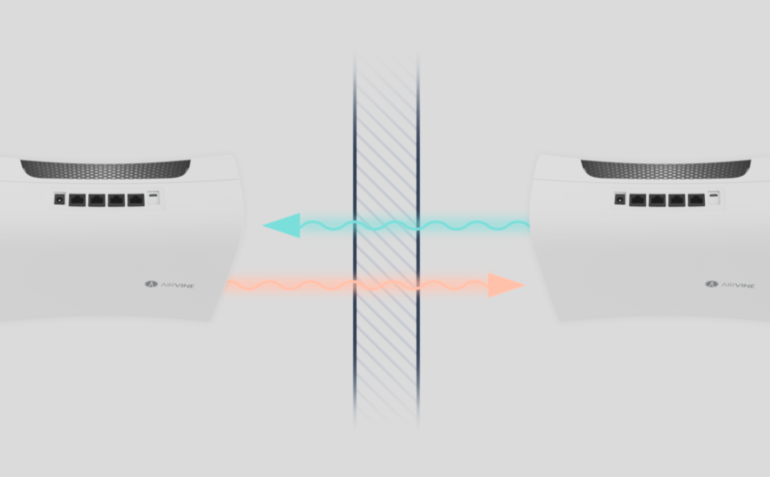
Connecting the Unconnected
Richard Bennett0
John Horrigan on Digital Inclusion
Richard Bennett0
Wheeler supports his own Internet regulations
Richard Bennett0
Some history on unlicensed spectrum
Richard Bennett0
Net neutrality advocates discover quality
Richard Bennett0
My op-ed in Fierce Wireless
Richard Bennett0
Progress on Spectrum Allocation
Richard Bennett0
Net Neutrality Reply Comments
Richard Bennett0
NTIA Spectrum Plan Implementation Comments
Richard Bennett0
HTF Comments on Title II NPRM
Richard Bennett0
DoD Drags Down the Spectrum Strategy
Richard Bennett0
FCC Lumbers Along with Net Neutrality
Richard Bennett0